设备标识符组合引擎 (DICE) 是已纳入 Android 的受信任计算机组 (TCG) 规范。 它会为启动序列期间加载的每段固件创建一组安全系数高的不可变加密身份。这些身份可用于远程验证设备的安全状况,而只有破解 ROM 才能规避这种验证。
DICE 派生过程
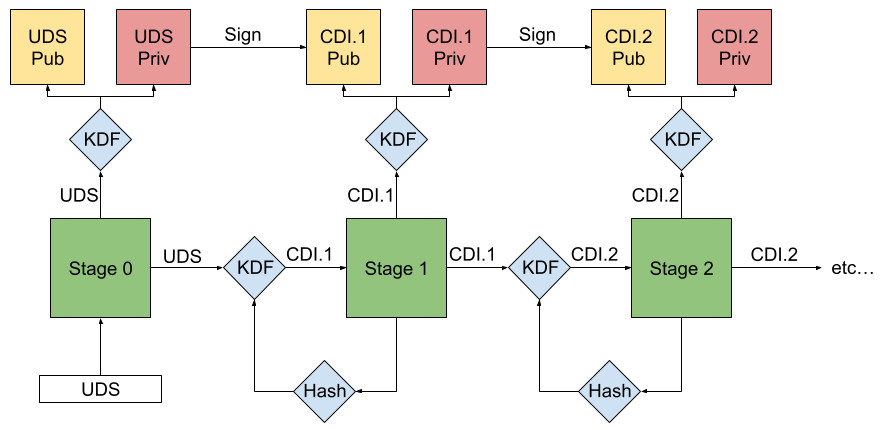
图 1. 简化的 DICE 派生过程。
DICE 派生过程可确保对任何固件映像进行的任何更改都会为该阶段和后续的每个阶段生成一个新的唯一标识符。这是因为每个已加载的固件阶段都会对下一个阶段进行测量和认证,生成唯一的身份和关联密钥,以防止绕过或篡改。只读存储器 (ROM) 会使用密钥派生函数 (KDF) 处理测量、配置和唯一设备 Secret (UDS),以便为要加载的下一个阶段派生 Secret。此 Secret 称为复合设备标识符 (CDI)。
第 0 阶段:初始化
DICE 流程始于芯片组的 ROM 从一组不可变数据(通常是熔断器)加载 UDS。此 UDS 会在芯片生产过程中使用加密随机值进行安全预配。读取 UDS 后,ROM 会使用供应商相关的硬件锁定机制(例如锁存器)锁定 UDS 访问权限,直到下次启动。
第 1 阶段:派生初始密钥
ROM 使用 UDS 作为密钥推导函数 (KDF) 的输入,以生成唯一标识该设备的永久性非对称密钥对。它会测量下一个固件阶段,包括有关启动环境的元数据,例如是否启用了安全启动。然后,ROM 会合并 KDF 中的 UDS、固件测量和配置数据,以派生第一个 CDI,并将其作为 Secret 传递到下一个阶段。
第 2 到第 n 阶段:派生递归密钥
然后,重复此过程。在所有后续阶段,上一个阶段的 CDI 都将作为新 KDF 的输入。此 KDF 使用 CDI 和下一个固件映像的哈希值来生成新的派生 CDI。每个阶段都会生成自己的密钥对,并使用该密钥对对包含阶段专属测量数据和其他关联元数据的证书进行签名。
