为确保车载系统的完整性,Android Automotive 会在以下级别保护传入的数据:
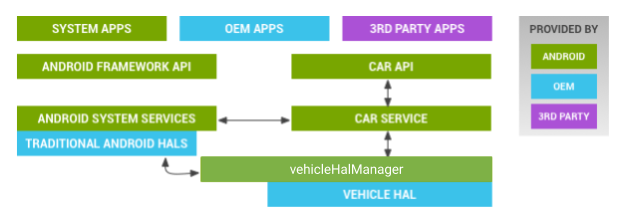
图 1. 系统服务架构
- 应用。系统会验证某应用是否有权与车载子系统通信。
- 明确定义的 API。通用 API 不接受任意数据 blob(必须对 API 进行明确定义)。
- 汽车服务。只能在启用全盘加密和启动时验证的情况下通过 OTA(或 USB)进行更新,无法旁加载。
- 车载 HAL。确认特定消息已获许可。
应用和 API
Android Automotive 基于 Android 构建而成,可直接与大量关乎安全的子系统交互。此外,不同车型可能会采用不同的接口,面向 Android 的功能也有所不同。为了确保这些功能可安全运行并对其进行精简,系统会在抽象层将其与 Android 的其他部分隔离开。仅明确定义且对通过车载网络发送的消息设置了严格格式的 API 可与车载 HAL 通信。这不仅为 Android 开发者提供了可预测接口,还可确保与车辆的其他部分安全交互。
系统会在以下两个级别对车载 HAL 消息进行过滤:
- 应用级别。非系统应用可通过具有适当权限的汽车服务访问车载 HAL。
- 车载 HAL 级别。可额外增加一层保护并确保发送至车载子系统的消息来源合法。也可用于限制消息速率,以防恶意应用使用泛洪攻击 CAN 总线以及对车载子系统造成干扰。
车载 HAL
车载 HAL 是与车辆交互的较低层,旨在通过驱动程序输入/输出控制 (ioctl) 调用与车载网络和其他车载硬件通信。
车载 HAL 是 Android Automotive 中唯一可连接到 IVI 系统的组件,可直接通过应用处理器/微控制器连接,也可通过 VMCU 以受限的方式连接。仅采用 SELinux 规则且对内核接口具有适当权限的系统应用可以访问车载 HAL。
SELinux 政策
Android Automotive 扩展了 SELinux 的适用范围,用于过滤驱动程序访问权限,包括 open、close、read、write 和 ioctl 调用。使用 ioctl 过滤(以及其他 SELinux 功能)可限制车载 HAL 允许和接受的 CAN 消息的类型,从而大大缩小了受攻击面。如需详细了解 SELinux,请参阅 Android 中的安全增强型 Linux。
此外,车载使用场景包括应隔离和控制的新型敏感数据。敏感数据具有单独的权限;HVAC 控制和窗户调整等其他功能应仅供系统应用使用。Automotive 专属 SELinux 政策示例:
<permission-group android:name=”android.support.car.permission.CAR_MONITORING /> <permission android:name=”android.support.car.permission.CAR_MILEAGE” android:protectionLevel=”signature|privileged” /> <permission android:name=”android.support.car.permission.CAR_SPEED” android:permissionGroup=”android.permission-group.LOCATION” android:protectionLevel=”dangerous” /> <permission android:name=”android.support.car.permission.CAR_VENDOR_EXTENSION” android:permissionGroup=”android.support.car.permission.CAR_INFORMATION” android:protectionLevel=”signature|privileged” />
为汽车相关权限创建了 CAR_MONITORING 权限组。可将当前速度视为敏感信息。因此,创建了保护级别为“危险”的 CAR_SPEED 权限。该级别表示信息涉及隐私且敏感。创建了具有系统级或签名级权限的 CAR_VENDOR_EXTENSION 权限,可用于已明确获得此权限的系统应用或已签名的应用。
应用和 activity 屏蔽
为使驾驶员在驾驶过程中少分散注意力,Android Automotive 提供了一些额外的控件(许可名单),以确保旁加载的应用在车辆行驶时不可用。这些应用在熄火或停车后仍可运行。
许可名单用于指定在车辆行驶时使用哪些应用。只有受信任的系统应用才能更新许可名单。尽管可以通过网络进行更新,但不应将此类更新视为可靠更新。
