对于搭载 Android 13 或更高版本的设备,Android 支持首次使用时信任 (TOFU) 身份验证方法 (RFC7435),让用户能够信任企业 (EAP) 网络,方法是安装服务器使用的根 CA 并在已保存的网络中设置其域名。借助 TOFU,设备可以在用户首次连接到某个企业网络时获取未经身份验证的公钥,并保留该公钥以在后续连接时使用。
背景
与仅需要密码的个人网络相比,企业网络使用公钥基础架构 (PKI) 身份验证方法,该方法需要客户端预安装相关证书。在 Android 11 或更低版本中,用户可以在网络设置中为服务器 CA 证书选择“不验证”选项,以绕过服务器端证书验证。不过,为了增强安全性并遵守 WPA R2 规范,Android 12 针对企业网络引入了服务器证书验证要求。这项附加要求为用户设置了屏障,因为他们需要为此类网络安装 CA 证书。借助 TOFU,用户只需接受基于 PKI 的企业网络的根 CA,即可连接到相应网络。
功能行为
在用户连接到没有已安装且经过身份验证的公钥时,支持 TOFU 的设备会表现出以下行为。
通过 Wi-Fi 选择器连接到新网络
在 Wi-Fi 选择器中选择新的企业网络。
设备会显示一个对话框(图 1),用于确认网络是否可信。
点按是,连接即可接受网络连接,或点按否,不连接即可拒绝连接。
如果您点按是,连接,设备会自动配置安全参数,连接到相应网络,并针对相应网络启用自动连接功能。
如果您点按否,不连接,设备会与相应网络断开连接,并针对相应网络停用自动连接功能。
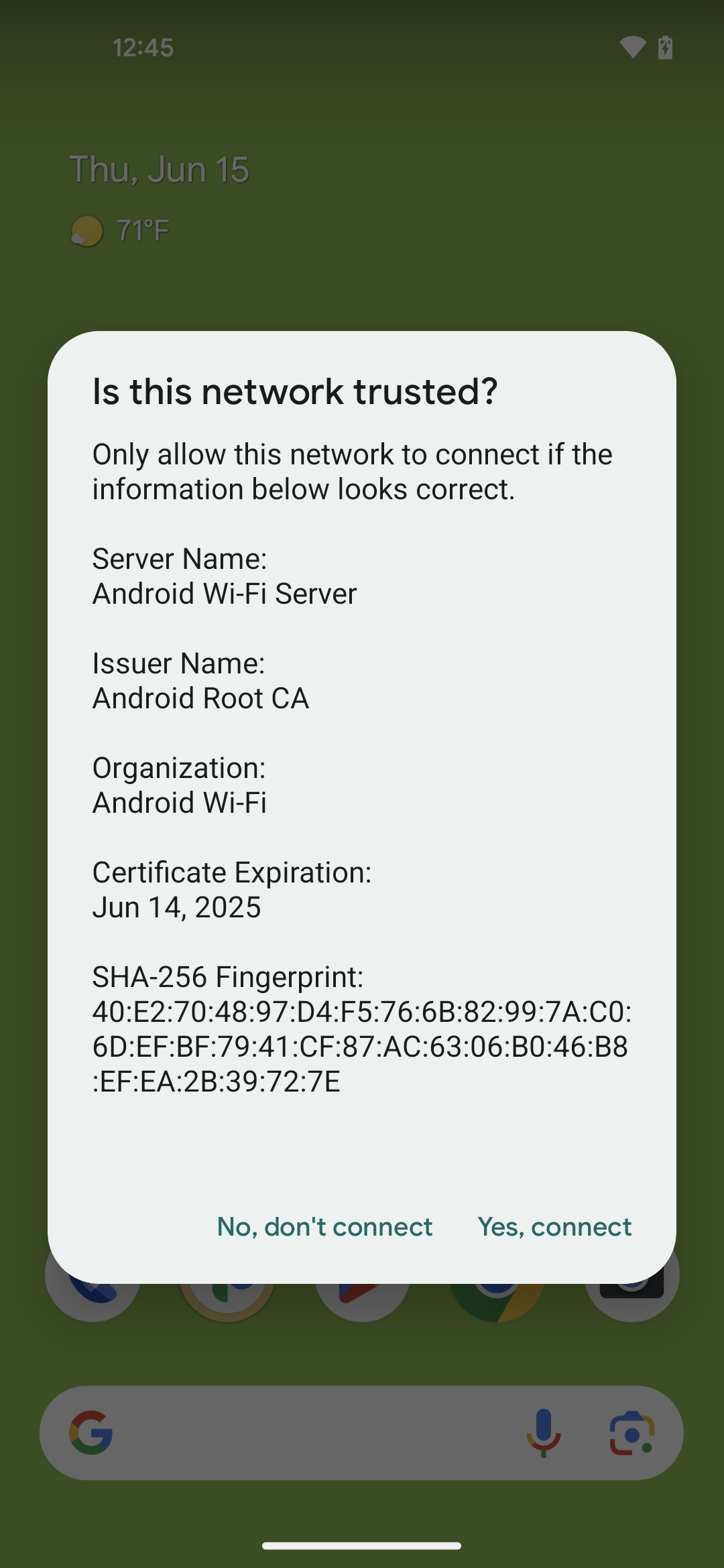
图 1. TOFU 功能的对话框
连接到已启用自动连接功能的现有网络
在连接到已启用自动连接功能但缺少有效 CA 证书的企业网络时,设备会自动连接,然后显示固定(不可关闭)通知。
点按通知。
设备会显示一个对话框(图 1),用于确认网络是否可信。
点按是,连接即可接受网络连接,或点按否,不连接即可拒绝连接。
如果您点按是,连接,设备会自动配置安全参数,连接到相应网络,并针对相应网络启用自动连接功能。
如果您点按否,不连接,设备会与相应网络断开连接,并针对相应网络停用自动连接功能。
实现
如需支持 TOFU 功能,请实现 Android 开源项目 (AOSP) 中提供的客户端 HAL,网址为 /hardware/interfaces/wifi/supplicant/aidl/android/hardware/wifi/supplicant。
Android 13 中提供了可供应用使用的以下公共 API:
WifiManager#isTrustOnFirstUseSupported():用于指示设备是否支持 TOFU。WifiEnterpriseConfig#enableTrustOnFirstUse(boolean):用于启用 TOFU。WifiEnterpriseConfig#isTrustOnFirstUseEnabled():用于指示是否已启用 TOFU。
验证
如需验证 TOFU 在您的设备上的实现情况,请使用以下测试:
- CTS:
CtsWifiTestCases - VTS:
VtsHalWifiSupplicantStaNetworkTargetTest
